Why Stronger Email Security Matters More Than Ever
One of the most common questions we hear from clients is whether advanced email security is really necessary. After all, if your team only notices a few suspicious emails each month, it can be easy to assume your current protection is enough. Some businesses wonder if adding another layer of email security, particularly impersonation protection, is worth the investment.
The short answer? Absolutely.
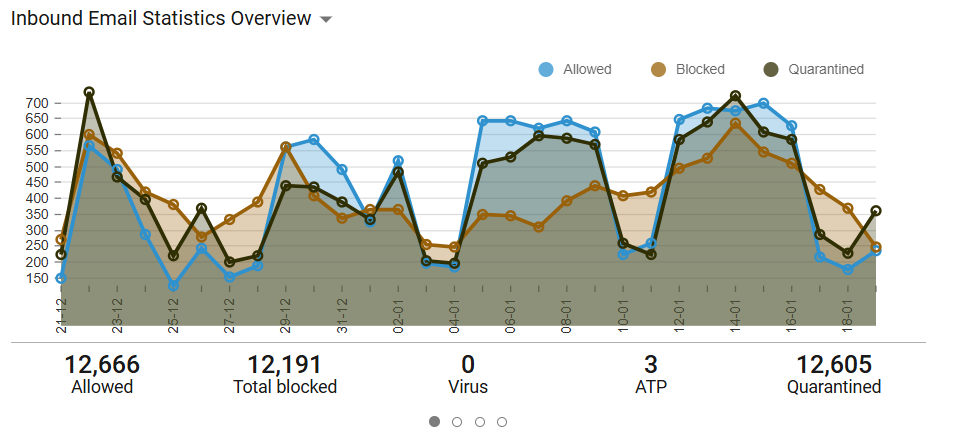
In fact, many organizations are surprised to learn just how many threats are already targeting them behind the scenes. After reviewing one client’s monitoring reports over just 30 days, we found that nearly 24,000 emails came into their environment, (see graphic) and almost half of them were spam, phishing attempts, impersonation attempts, or other malicious threats.
Half.
That’s not unusual anymore.
Nearly 45% of global email traffic is considered spam, and malicious email attacks continue to rise year over year. If your users are only noticing a handful of suspicious emails, it usually means your security tools are working, not that attackers aren’t trying.
Why Impersonation Attacks Are So Dangerous
Today’s phishing emails look very different from the obvious scams people used to expect. They are often polished, personalized, and designed to appear as though they came from someone your team knows and trusts, a CEO, CFO, payroll provider, vendor, or even your internal IT department. This is known as Business Email Compromise (BEC), and it has become one of the most expensive forms of cybercrime. In many cases, attackers are not trying to install malware. They are trying to create urgency and trust.
“Can you process this wire transfer before noon?”
“Please review this secure document right away.”
“Your password has been compromised, please reset it immediately using the link below.”
These messages look normal, which is exactly why they work. Recent reporting shows that impersonation accounts for the majority of BEC incidents, and CEOs are among the most commonly impersonated targets. Leadership teams are often the primary focus of these attacks, which is something we see regularly in real-world environments.
What Impersonation Protection Does Differently
Traditional spam filters focus on obvious threats like malicious attachments, known spam domains, and suspicious links. While that protection is important, it does not always catch the more convincing impersonation attempts.
Impersonation protection goes further by identifying subtle warning signs that something isn’t right, including:
- Display name spoofing
- Lookalike domains
- Executive and vendor impersonation
- Internal email spoofing
- Conversation hijacking
- Unusual sending behavior
Instead of simply asking, “Is this spam?” it asks, “Does this email actually make sense coming from this sender?” That extra layer matters because the most dangerous emails are often the ones that look the most legitimate.
Small and Midsize Businesses Are Still Targets
Many business owners assume attackers only focus on large enterprises. Unfortunately, that’s not true. Smaller organizations are often attractive targets because they may have fewer approval processes, fewer security controls, and less formal security awareness training. Attackers know that urgency creates mistakes, and they count on someone reacting quickly before verifying a request. That’s why impersonation protection is so valuable. It helps stop risky emails before someone has to make a split-second decision.
The Bottom Line. Yes, Impersonation Protection is Worth It.
If you’re wondering, “Is impersonation protection worth it?”, the better question might be: “What would one successful phishing attack cost?” A fraudulent wire transfer, stolen credentials, ransomware event, or compromised payroll account can create damage far beyond the cost of prevention. Strong email security is not about eliminating every phishing email, it’s about reducing risk to your business. If you’d like to understand what’s actually hitting your inbox, and whether your current protection is enough, we’re always happy to help review your email security posture.
Because when it comes to phishing, what you see is usually only a small part of the story.
Reader Interactions