In the recent news, we read about a UMaine professor whose laptop was stolen from a checked suitcase while he was traveling. The laptop contained personal information of hundreds of current and former UMaine students, including social security numbers, phone numbers and email addresses. The university had a security policy in place that should have prohibited this sort of event from having such a negative widespread affect, but it didn’t. The events that have unfolded serve as a reminder of how vulnerable we are when laptops, smartphones and tablets are stolen.
We thought we’d take moment to quickly list a few ways you can protect yourself and your organization if this were to happen to you. We are always advocating for proactive IT plans, being sure to take steps BEFORE disaster strikes and in cases like this, being proactive is the only way to ensure data protection.
Don’t Violate Security Policies – it may be against the law
Security policies are in place for a reason. It protects your organization, those that your organization serves and you, personally! It is not always convenient to go through some of the steps but it is vital in order to protect data, and that is always worth it in the long run. Take the extra time to sit with your IT department to make sure your daily operations are not in violation. If your organization doesn’t have a security policy, work with a local, dependable IT firm that can accurately assess your risks and put systems in place to mitigate them. This is especially important for organizations that are regulated by federal law. “Federal law (HIPAA, HITECH, etc.) requires the protection of certain data and holds individuals as well as organizations responsible for implementing security to protect data from authorized access in the event of theft or loss of a device containing certain classes of sensitive data.” (OU IT)
Data Encryption for Laptops & Thumb Drives
Laptop encryption software encrypts your data so that it cannot be accessed without a decryption key or a password. This is vital to protecting your information if your laptop is ever stolen. If your data encryption is configured properly with strong passwords and private key, then chances are the person who stole your laptop won’t be able to access anything on it. In addition to laptops, be sure to also encrypt data stored on those thumb drives we all love so much. Even if you accidentally lose it, wouldn’t you feel better knowing your data was encrypted?
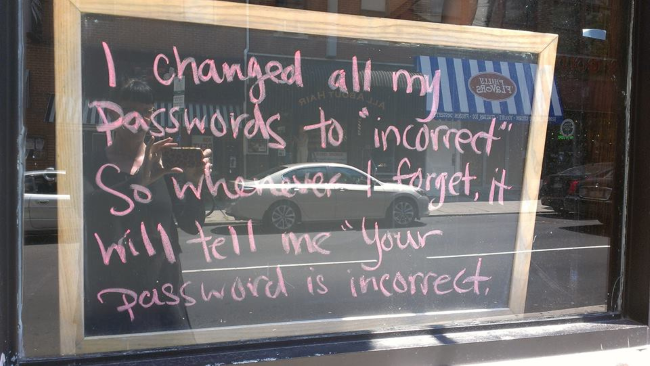
Strong Passwords
We get it. Passwords are a pain. You have different password requirements for different applications, user accounts, laptops and devices and that’s not even including all of your personal bank accounts and everything else you may use at home! One way to address this is NOT to write them down on a sticky note at your computer or in your laptop carrying case. Instead, read this HowtoGeek.com article on how to create strong passwords and remember them. In the first section of the article they suggested to choose a password that is 12 characters (don’t panic, you can do this!), includes numbers & symbols, capital and lowercase letters and that isn’t a dictionary word. Pick memorable items that others wouldn’t easily guess or know. Make a short phrase and then see which letters can be swapped out for a number or a symbol. The phrase “Strong Password”, for instance, could be come $tr0ngP4ssw0rd$.
Ability to WIPE the Device Remotely
Whether it’s your laptop, your Android or your Apple device, there are products and services the help you protect your data using a remote wipe technology. This means that once you learn of the lost or stolen device, you can fully wipe out your data and reset all things back to factory default without needing psychical access to the device (which is a good thing, since it’s lost or stolen!) “Wait – reset to factory default and lose everything?!” you ask?
Online Backup
As long as you have been backing up your data to a remote location, like a cloud-based online backup system, you will be able to get all of your data restored to a new device with no trouble at all. Online backup is one of the most important components of disaster recovery that many businesses fail to recognize, and quite honestly, it leaves us shaking our heads. You need a backup solution and equally important, you need to check to ensure that 1.) it’s working on regular basis and 2.) that you can restore from the backup. Too often we have seen customer’s who thought they were protected, only to find out that their daily backup file was corrupted and it left them with no options to recover their data.
In today’s hustle and bustle, we understand how hard it can be to slow down and put these security features in place. However, we guarantee you will be very happy that you did, should you ever find yourself in this position. Our team of highly skilled IT professionals are ready to meet the needs of your organization and to create a customized data security plan that works for you and your budget.
Reader Interactions