What is CryptoLocker ?
The CryptoLocker Ransomware is a software threat that affects Microsoft® Windows systems running Windows 8, Windows 7 and XP Operating Systems. It first surfaced in 2013 and has been wreaking havoc on computers and business across the globe since that time.
“[This] Ransomware is a type of malicious software (malware) that infects a computer and restricts access to it until a ransom is paid to unlock it,” according to the Department of Homeland Security (DHS), who released an updated US-Cert Alert on October 22, 2014.
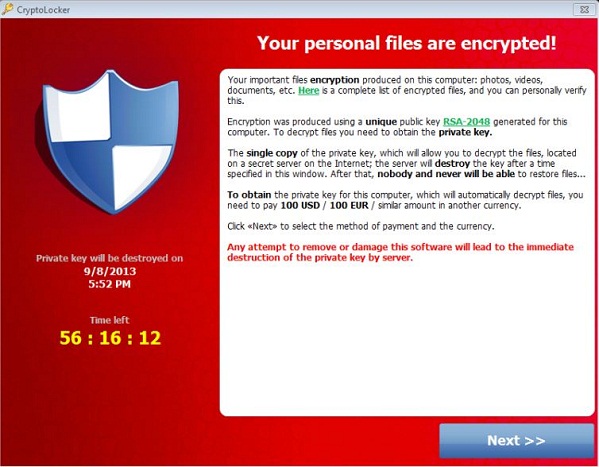
A computer infected by CryptoLocker will attempt to extort money from victims by displaying an on-screen alert stating that the computer has been locked or that all files have been encrypted. It then demands a ransom to be paid electronically in order to restore access to the files. Though the ransom varies it is typically in the range of $100–$300 dollars.
How do computers get infected with CryptoLocker?
The criminals behind this, and other, malicious software rely on fear and panic to trick end users into installing it without realizing what is happening. For instance, while browsing the internet or opening email an end user may see one of the following messages:
- “Your computer has been infected with a virus. Click here to resolve the issue.”
- “Your computer was used to visit websites with illegal content. To unlock your computer, you must pay a $100 fine.”
- “All files on your computer have been encrypted. You must pay this ransom within 72 hours to regain access to your data.”
Once the message is “clicked” the damage is done and the computer becomes infected, not only with CryptoLocker, but other malware as well.
The United States Computer Emergency Readiness Team website states: “Systems infected with ransomware are also often infected with other malware. In the case of CryptoLocker, a user typically becomes infected by opening a malicious attachment from an email. This malicious attachment contains Upatre, a downloader, which infects the user with GameOver Zeus. GameOver Zeus is a variant of the Zeus Trojan that steals banking information and is also used to steal other types of data. Once a system is infected with GameOver Zeus, Upatre will also download CryptoLocker. Finally, CryptoLocker encrypts files on the infected system, and requests that a ransom be paid.”
What affect does CryptoLocker have on businesses?
CryptoLocker is a threat to home computers and business computers alike but the ramifications of it can be more severe for businesses. When a business computer is infected by CryptoLocker, they may experience:
- Temporary or permanent loss of sensitive or proprietary information;
- Disruption to regular operations;
- Financial losses incurred to restore systems and files; and
- Potential harm to an organization’s reputation.
Paying the ransom does not guarantee the encrypted files will be released; it only guarantees that the malicious actors receive the victim’s money, and in some cases, their banking information. In addition, decrypting files does not mean the malware infection itself has been removed.
How to Protect Your Computer Against CryptoLocker
Be sure to perform reliable backups of your computer systems on a regular basis.
Then, test the backups to ensure that they are working properly. Oftentimes we have seen instances where businesses thought they were backing up their files but when the time came to make a restore from that backup, it was no good. At that point, there is not much that can be done and the data is lost. Cloud Backup Solutions are becoming the preferred backup method for businesses due to ease of use, monitoring, scalability and cost.
Use a reliable anti-virus software and keep the virus definitions updated.
A common misconception of anti-virus software is that once it is installed you are covered. However, anti-virus software needs to be updated in order to be effective and to protect against new threats that are continually being released. Managed IT Services eliminate the need for business owners to worry about this and other network maintenance.
Install updates to Microsoft® Windows Operating Systems any desktop software that is utilized by your business.
These updates contain security patches as well as enhancements to your software. Microsoft® Windows XP has been discontinued and Microsoft® Server 2003 will see the end of support in July 2015.
Schedule your Windows operating system upgrade now to prevent being left with outdated (and at-risk) software.
Do not click on links in emails that are unsolicited or from an unknown sender.
Even emails from “known” senders should be treated with the utmost diligence. If you are even remotely skeptical, don’t click on it! Read Avoiding Social Engineering and Phishing Attacks
Use extreme caution when opening attachments.
Read this article to learn how you can avoid email scams. Bottom line is, don’t open it if you don’t have to.
When browsing the web, use safe guidelines.
Don’t visit gambling sites, gaming sites, coupon sites or allow websites to install software on your computer. If you find yourself in a risky situation, call the IT HelpDesk immediately.
Evaluate Your Security Settings.
When was the last time you checked your security policies or tested your network configuration to ensure you and your mission critical data is fully protected? A Vulnerability Scan can show you areas that you may not realize are putting you at risk so that you can avoid potential disasters.
What to do if you are infected with CryptoLocker
Whether it is CryptoLocker or another type of malware or virus, please contact our IT Support HelpDesk immediately. Our certified helpdesk professionals are ready to assist you in any way possible.
Source: US-Cert Crypto Ransomware
[…] have seen a number of businesses affected by Cryptolocker or Cryptowall ransomware. Often, if the business does not have a reliable file backup, they are forced to pay a ransom and […]