Safe Computing is the first line of defense in Computer Security
At Burgess Computer, we understand that computer security is a top priority in today’s world. We regularly host computer security workshops. Today, we’d like to share that information with you. Included in this article you will learn:
- A series of best computer security practices you can follow to help protect your computer networks
- Awareness of potential online threats and how to recognize them
- How to keep up to date on the latest (and ever evolving) computer security threats & how to avoid them
Use Good Passwords
Passwords are the first line of defense when we are talking about computer security.
- Passwords should be minimum 7 characters or longer. The longer the better.
- Passwords should contain at least one alpha character(a-z).
- Passwords should contain at least one non-alpha character (!, @, #, $, %).
- Passwords should be a mix of upper and lowercase.
- Passwords should contain at least one number (1-9).
Example of a bad password: frank123
Example of a good password: !like2EatChicken
Password Security
Now that you have a strong password, here are a few ways to keep it safe.
- Never share your password.
- Never write your password down.
- Never email a password.
- Change your password periodically.
- Choose complex security questions.
- Stored passwords should be encrypted with an application, such as KeePass. Visit Best Practices for Safe Password Storage for in-depth information.
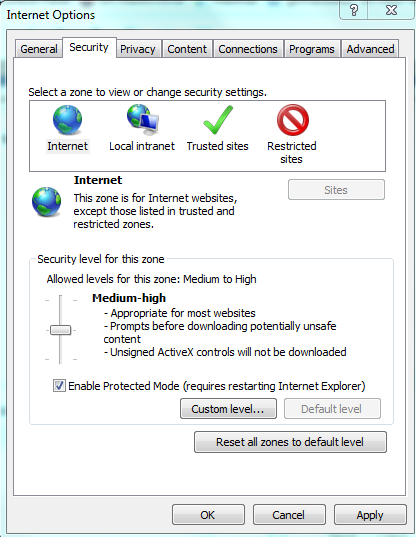
Use a Secure Internet Browser
Browsing the internet is risky business. Be sure you are staying safe.
- Keep your browser updated
- Keep security settings at recommended levels
- Use trusted sites when decreased security is needed
Avoid browser add-ons
Browser add-ons are one of the biggest culprits; often adding spyware and malware without you realizing what is happening.
- Don’t install browser add-ons or toolbars unless necessary
- Avoid “free” browser plugins on gaming or gambling websites
- Be mindful of legitimate software “updates” that might include these (see highlighted check marks below on what to watch for)
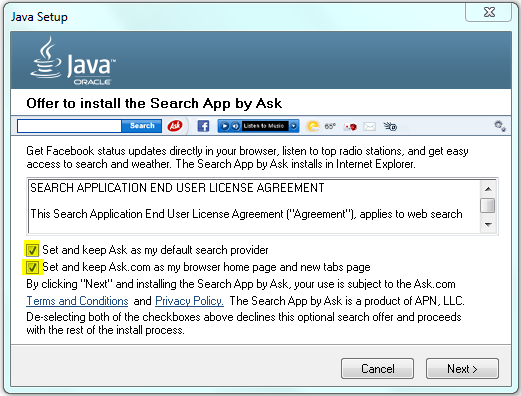
Uncheck Add-On Software that may be harmful to your computer security
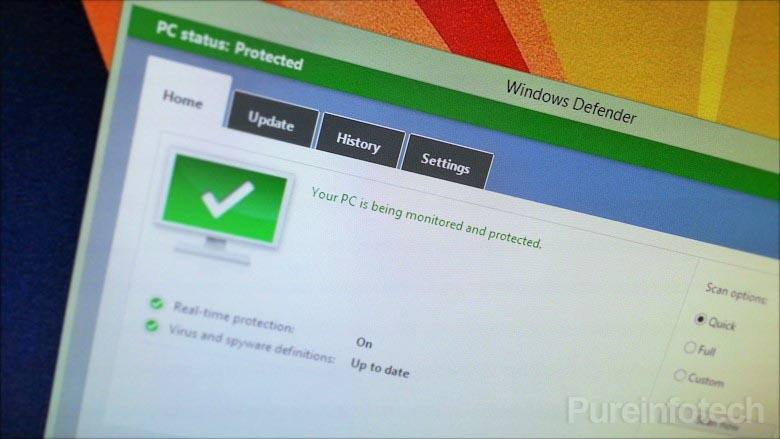
Antivirus
An important defender in computer security is a reliable and trusted Antivirus program.
- Use a recognized business antivirus
- Sophos, Managed Antivirus, Kaspersky, McAfee, Symantec, Security Essentials
- Manage PC’s using a central console
- Configure to update daily, and monitor this
- Run scheduled scans
- Pay attention to warnings and alerts
- Know when it expires –and renew it
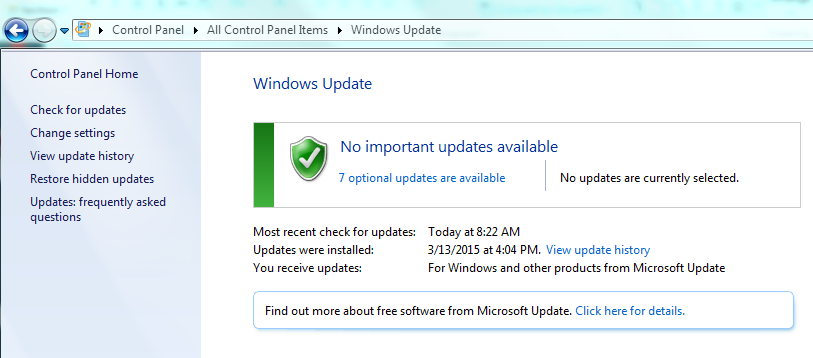
Install Updates for Windows®, QuickBooks® & Applications
- Install Operating System updates
- Install application updates (Adobe, Office, QuickBooks)
- Monitor update status on all computers
- Don’t use outdated operating systems or software
- Microsoft Windows XP, Microsoft Server 2003
Use a Reliable Backup System
Use a modern backup system to ensure any compromise of your files will not result in data loss!
- Run monthly test restores and monitor backup status daily
- Review what’s backed up quarterly to ensure all critical data is captured
- Keep a backup locally and offsite
- Consider recovery times
- Backup is the only recovery method for Ransomware such as Cryptolocker!
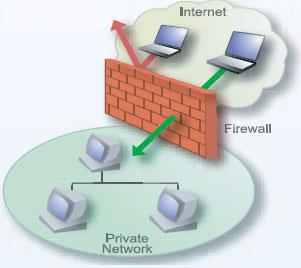
Use a layered security approach
Layered computer security allows different technologies to filter internet traffic, reducing single point of failure.
- Install a business class firewall
- Brands such as Cisco, SonicWall, Fortinet
- Has advanced security features such as Intrusion Prevention, Gateway Antivirus and Antimalware
- Uses web content filtering
- Professionally installed
- Use mail protection that filters SPAM and Viruses before they reach you
- Use desktop Antivirus and Antimalware
- Monitor devices for repeated failed logins or unusual activity
Vulnerability Scanning
Vulnerability Scanning has become a useful tool that scans your network for potential weaknesses.
- Vulnerability Scanning provides report of findings
- Allows for corrective action to be taken
- Next, another scan is performed to confirm remediation
- This is required for Payment Card Industry (PCI) compliance
Train your staff on safe computing habits
This should be an on-going effort. Talk with your employees about computer security regularly.
- Do not share passwords or send them in email or text files
- Do not open unknown email attachments from unknown senders, and be wary of unexpected attachments from known senders
- Do not save, install or run software downloaded from the Internet unless it has been scanned for viruses
- Have a computer use policy and review it with your staff
- Be wary of phone calls claiming to be from an IT vendor. Confirm identities before giving out any information.
- Keep internet browsing to business related activities only
- Avoid giving users “administrative” privileges on a computer
- Beware of pop ups, strange emails, and odd phone calls.
Beware of the “official looking” warning
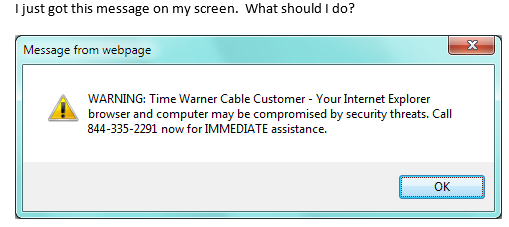
- Do NOT click OK or Remove, this can cause a virus to infect
- “End Task” on your browser using task manager
- Turn off computer if infection is suspected
- Contact your IT service provider
Beware of the “too good to be true” trick
- Becoming more popular and targeting specific users, such as CFO or IT
- Never open attachments from unknown senders
- Never open unexpected attachments from known senders
- Delete the message
Beware of the “sneaky link” tactic
Also known as phishing or spear-phising
- Never click through links from unknown senders
- Never click through unexpected links from known senders
- “Mouse over” (but do not click) the link to see the real destination
- Beware link shortenerslike tinyurl.com or bitly.com, ex. http://tinyurl.com/pb7gug5
- Delete the message
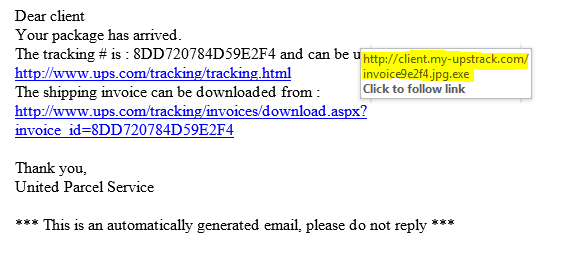
DON’T CLICK!!
Beware of Drive by Downloads
Drive by downloads are found on malicious websites and automatically redirect you to a malware installer. This is often the most difficult security thread to defend against because if often requires NO user interaction, it just happens automatically.
- Might pose as legitimate software or antivirus
- You can get out of it by clicking “End Task” on your browser using Windows Task Manager
- Turn off computer if infection is suspected
- Contact your IT service provider before your computer is turned on again
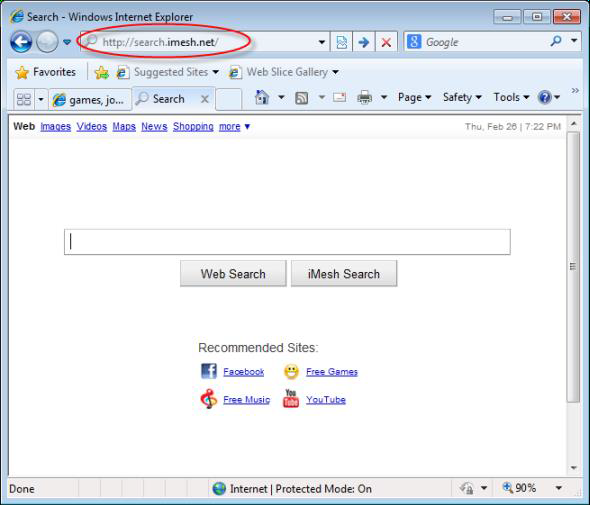
Beware of the “search hijacker”
The search hijacker redirects your browser to another search engine.
- Could lead to additional malware infections
- Turn off computer if infection is suspected
- Contact your IT service provider
The “Ransom” aka Cryptolocker or Cryptowall
We have seen a number of businesses affected by Cryptolocker or Cryptowall ransomware. Often, if the business does not have a reliable file backup, they are forced to pay a ransom and then hope the hackers return their data, though there is no guarantee.
- Infects by clicking link or opening attachments
- Encrypts certain file types like QuickBooks, databases
- Network aware, can encrypt shared files
- The only remedies are to pay the ransom or restore from backup
Keep up with current threats
- US-CERT –Computer Emergency Readiness Team
- Sophos
- Alerts and news specific to your trade, ex. http://www.bankinfosecurity.com/
- Burgess Computer –sign up for our newsletter and receive security alerts, news & more
Reader Interactions