The latest threat to your personal and business computers has arrived. Zepto is the latest form of ransomware that is wreaking havoc on computer systems far and wide. It’s similar to the CryptoLocker ransomeware we have seen in the past.
How Zepto Arrives
It arrives as an attachment in an email. Once a user double-clicks the attachment to open it, the computer becomes “infected” with this malware.
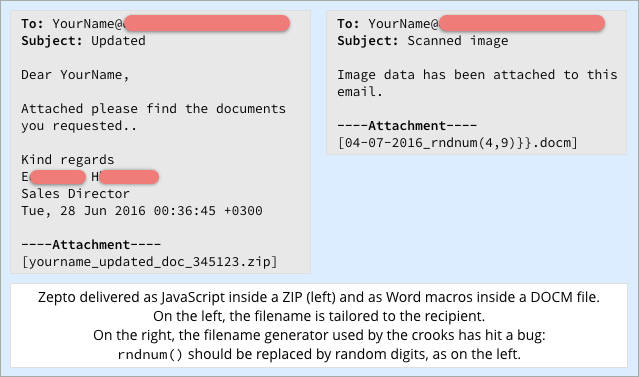
Image Source: Sophos
What Zepto Does to Your Data Files
When a computer is infected with Zepto, the malware encrypts your data files so that they can only be accessed with a decryption key. To gain access to the decryption key, users must pay a hefty ransom to the Zepto computer crooks. Think about all the documents, spreadsheets, programs and more that you rely on every day. What would you do if in an instant, you no longer had access to them. It can be devastating for a business of any size.
What You Can Do to Protect Against Zepto
An ounce of prevention with worth a pound of cure
- Be sure that you have a solid backup system in place.
- Ensure the backup is running successfully.
- Ensure that the backup includes all of your mission-critical files.
- Test your backup regularly to ensure that a restore will work if it’s ever needed.
- Be suspicious of any email attachment that is received
- Understand that ransomware can come from people you know and people you don’t know
- Do not open any attachment you are not expecting, even if it’s from someone you know or work with.
- Understand that these crooks are sophisticated and can use social engineering and spear-phishing to trick you.
- Be quick to react if you think you’ve become infected
- Shut down your computer immediately
- Physically disconnect it from any network you are connected to
- Contact your network administrator or our IT Help Desk immediately
- Be Proactive
- Share this news with co-workers, employees, friends & family
- Share this news with the elderly and people who may be more susceptible to falling prey to this sort of scam.
Read more about computer security and ransomware:
No Deal for Ransomware Hackers Thanks to Cloud Backup
Computer Security: Best Practices
Reader Interactions